Looking back at 2022 we are analyzing what has changed in the market and how this will marketers in 2023. ClickSpam has risen in popularity in 2016 and has since then had some developments which made it more effective for fraudsters. In this article we will describe the development over the years.
There is one method by which fraudsters poach organic users when it comes to ad fraud techniques. This type of fraud, known as click spam, occurs when a fraudster executes clicks for users who did not make them and claims credit for random installs the user made. It begins when a user lands on a mobile web page or an app operated by a fraudster. From there, one of several types of click fraud could occur:
The mobile web page may be carrying out mobile click fraud in the background without visible ads or ads that can be interacted with. The spammer could start clicking in the background while the user is using their app, giving the impression that they have interacted with an advertisement. If the fraudster app is running in the background at all times, it can generate clicks at any time (e.g. launchers, memory cleaners, battery savers, etc.)
Click Spam is attribution Fraud generated by a large amount automated / fake clicks to steal conversions from organic traffic and other legitimate traffic sources.

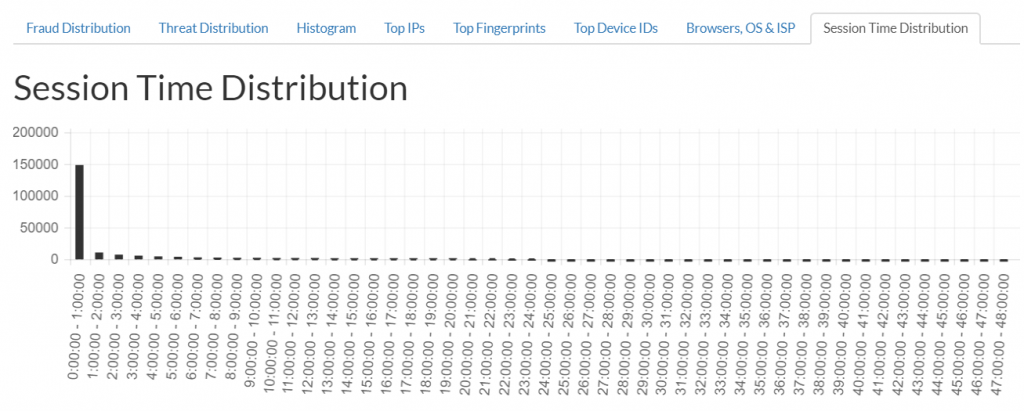
Normal CTIT Distribution – Session Time Distribution
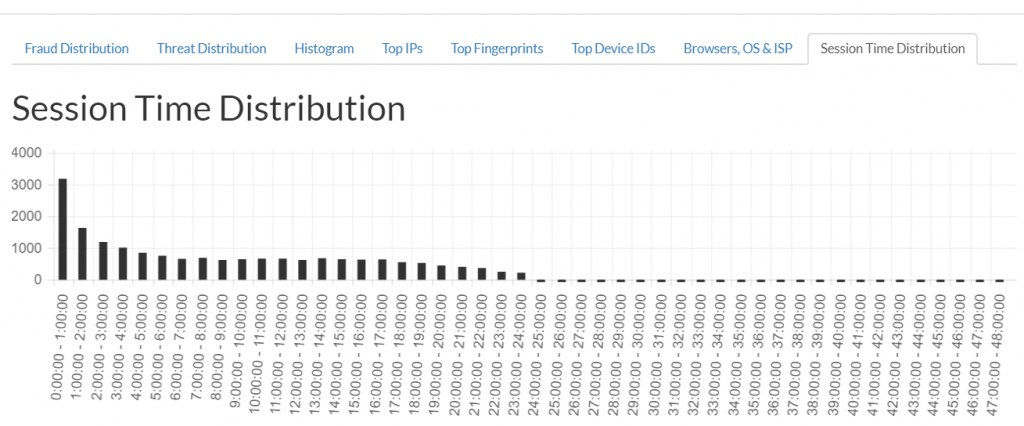
ClickSpam CTIT Distribution – Session Time Distribution
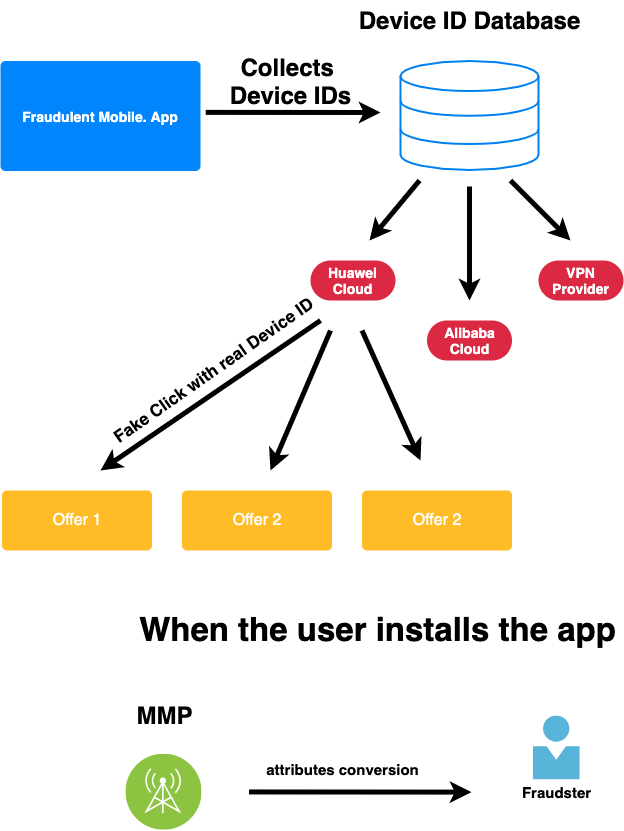
In 2021 a new more aggressive tactic evolved. During our Click Analysis of Clicks we have noticed a new schema using Bot generated clicks with real device IDs to showing an unusual high amount of VPNs at Click Level.
The difference from previous ClickSpam is that clicks are not triggered from the Mobile Device but instead from Bots with real Device IDs previously collected through a malicious app. These clicks include a Device ID which gets stored on the MMP side and when the user installs the app – the conversion will be attributed to the Fraudster.
By running his own database of real Device IDs the Fraudster has two advantages:
- Full control when a click should be triggered.
- No direct access to the device needed.
- Ability to spread his fake clicks across as many apps.
- Conversion IPs are reported from the Install IP not the Click IP and then show as a non VPN related IP-Address
What can be done against this new type of fraud ?
Sources with high amounts of VPN / Server side clicks shall be blocked before reaching the MMP / advertiser. We strongly recommend looking into the the ClickStreams of sources.